
Using Security Awareness to Empower Your Most Important Assets
July 30, 2020
“Don’t fire the CISO”, with Quentyn Taylor
July 31, 2020SMB Cybersecurity: More products, more problems?
The importance of a simplified approach to security
As cybercriminals continue to find new ways to breach security defenses, keeping your organization secure may start to feel overwhelming. Security teams are constantly striving to stay ahead, but it can be difficult to decide what to prioritize. So, in a sea of new security products and recommendations, how can small and medium sized businesses decide where to invest their finite resources?
In a recent Cisco Chat Live streamcast, Cisco Product Marketing Manager Hazel Burton, Cisco Advisory CISO Wolf Goerlich, and Elevate Security Co-founder Masha Sedova sit down to discuss ways of cutting through the noise and simplifying security.
More products, more problems?
Wolf Goerlich describes an outage he and his team faced in a previous organization, during which their remediation was complicated by too many alerts:
“The security guy comes back and says, ‘It’s clearly a denial of service.’ I said, ‘Alright. That kind of makes sense with your data.’ The networking guy goes, ‘Wait a minute. We think the problem is on the edge because we’re not seeing many packets.’ The compute guy says, ‘No, the problem is clearly on our servers because the CPU is spiking right now’…. The entire outage got stretched out just trying to get everyone on the same page with all of these counsels on these data points.”
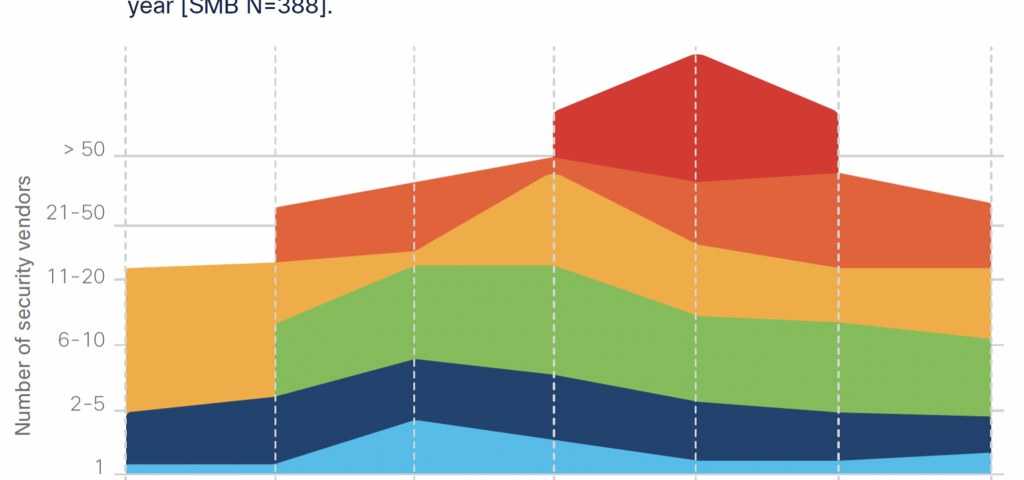
This anecdote is also supported by a survey we conducted across almost 500 SMBs (defined here as organizations with 250-499 employees). Respondents were asked to report the number of hours lost during the most severe security breach faced in the past year. This was correlated with the number of security vendors their organization uses.
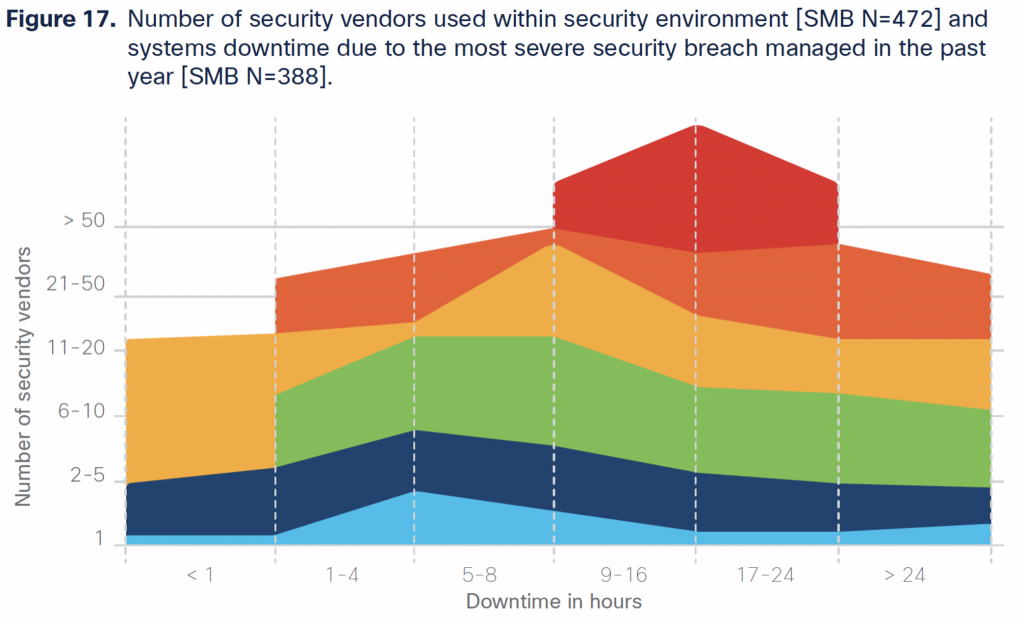
Surprisingly, it appears that the more vendors an organization used, the less effective those tools were in mitigating a severe breach. In fact, organizations using 2-5 vendors had an estimated downtime of around 5 hours, while organizations using 50 or more vendors reported an average downtime of about 17 hours.
While there are a multitude of reasons behind why certain breaches cause longer downtimes than others, the complexity of trying to compile data across many vendors and tools seems to be a contributing factor.
The importance of not exceeding your team’s “cognitive maximum”
This data suggests that security teams have a limit to the number of tools they can feasibly juggle before reaching what Wolf coins as their “cognitive maximum.” When security teams are asked to use an overwhelming number of products, they may not be able to pinpoint where an issue lies.
Unfortunately, security teams that feel inundated by tools and disparate data can experience cybersecurity fatigue – or the feeling that they simply can’t keep up with incoming threats. To learn more about the symptoms of cybersecurity fatigue and how it can be managed, check out the clip below.
Homing in on the solutions that will best help you
To avoid overwhelming security teams, Masha Sedova recommends focusing on the threats your organization is most vulnerable to experiencing. Getting to know which threats most impact you and prioritizing accordingly is a great way to simplify your security approach, and may help when deciding which solutions are worth investing in.
Masha suggests using tools like the Verizon Data Breach Investigations Report to determine which risks to consider targeting. In the second installment of our SMB Cybersecurity Series, we discussed the SMB threat landscape. You can see our findings on which threats SMBs are currently facing here. Additionally, Cisco’s Threat of the Month series recently dedicated a post to the remote work threat landscape, which can be found here.
Keeping it simple by focusing on the basics
One of the best measures to keep your security program as simple as possible, as Masha recommends, is making sure the basics are covered. Knowing which data is stored where, for example, can be extremely helpful in determining where an attack is coming from.
With a solid foundation and a good understanding of what to prioritize, you may find it easier to incorporate relevant security solutions without adding undue complexity. For more tips on simplifying your security operations, check out the clip above. To watch the full Cisco Chat Live discussion, please visit Cisco Chat Live SMB Myth Busting.
Note: This blog is the last in a five-part series.
You can read the previous blogs in our SMB Cybersecurity Series here.
If you are interested in unpacking more myths surrounding SMB security, consider reading “Big Security in a Small Business World.”
The post SMB Cybersecurity: More products, more problems? appeared first on Cisco Blogs.

