
Mitigating Dynamic Application Risks with Secure Firewall Application Detectors
September 24, 2021
Control Across Your Hybrid Environments Using Cisco Secure Workload 3.6
September 28, 2021Cisco Interop: Discovery of Designated Resolvers Protocol Implemented
Earlier this year in a blog post, I shared a bit about our Auth-DoH idea. In case it’s not top of mind, let me help refresh your memory. Auth-DoH is essentially a safer way to publicly advertise private services. It’s a forward-looking idea to improve DNS security.
Another forward-looking idea is Discovery of Designated Resolvers (DDR). DDR allows for upgrading from insecure DNS to secure DNS. I am proud to say Cisco Umbrella is the first to implement support of the new IETF protocol. And there’s more. We are extending an open invitation for vendors to test their DDR solution against our production systems and report any issues.
As the pioneers of secure DNS, Cisco Umbrella is once again at the forefront of policy enforcement and interoperability – ultimately making DNS more secure. Don’t just take my word for it, you can test it out yourself in our open interop. After you try it, be sure to tell us what you think.
DDR Interop Details
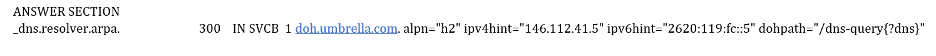
If your network DHCP settings are configured to provision 146.112.41.5 or 2620:119:fc::5 as the IP address of the DNS Resolvers for your network, the DDR protocol will allow DDR-complaint devices to automatically upgrade from traditional DNS (Do53) to the more secure DNS over HTTPs (DoH) protocol on the same IP address automatically.
If everything works as expected you should see a response from our resolvers that look something like the following:

The new DDR protocol capability allows for two important things to occur. First, the network still acts as a policy enforcement point and secondly DNS is more secure for both the enterprise and end user.
DDR & DoH provide for an end-to-end privacy-preserving secure DNS solution and Cisco is a strong advocate of leveraging Encrypted DNS technologies. In fact, Cisco Umbrella has offered Encrypted DNS capability using the DNSCrypt protocol for more than a decade. With the addition of DDR, DoH can now provide many of the same capabilities found in the Cisco Umbrella DNSCrypt solution.
We have enabled DDR on the following Cisco Umbrella systems for interop testing:
146.112.41.2 / 2620:119:fc::2 · doh.opendns.com
146.112.41.3 / 2620:119:fc::3 · doh.familyshield.opendns.com
146.112.41.4 / 2620:119:fc::4 · doh.sandbox.opendns.com
146.112.41.5 / 2620:119:fc::5 · doh.umbrella.com
What’s Next
Please feel free to try one or all the options above and send any feedback to ddr@cisco.com. We look forward to the interop engagement and continued work in IETF in support of Encrypted DNS capabilities at Cisco.

