
Autodesk Introduces the Next Generation of Tools for a New Era of Infrastructure
April 15, 2022
Security Resilience in EMEA
April 20, 2022Cisco Secure Endpoint Shines in the 2022 MITRE® Engenuity ATT&CK Evaluation
Recently MITRE Engenuity released the results from its fourth round of the ATT&CK Evaluations. This round focused on threat actors Wizard Spider and Sandworm.
It’s no surprise that both hacking groups have made their presence felt. For example, between 2019 and 2020, Wizard Spider, a Russian-speaking cybercriminal group, extorted $61 million from ransomware attacks, including notable attacks that included Universal Healthcare System Hospitals, and state government administrative offices in both Georgia and Florida. In 2017, Sandworm infiltrated Ukrainian accounting software MeDoc and hijacked the company’s update mechanism which resulted in malicious software being introduced to copies of the MeDoc software used by its customers.
After participating in the 3rd round of MITRE Engenuity Evaluations, Cisco was excited to engage again to show our improvements over last year.
These evaluations are not a competitive analysis. MITRE shows the detections it observed without providing a “winner.” Because there is no singular way for analyzing, ranking, or rating the solutions, MITRE instead shows how each vendor approaches threat defense within the context of ATT&CK.
Cisco delivered strong results in the 2022 Evaluation
Overall, Cisco Secure Endpoint proved it can stop Wizard Spider and Sandworm attack campaigns early in the kill chains and provided analytic detections at the MITRE ATT&CK technique level across each step of its respective kill chains.
Summary of Cisco’s Results:
Cisco Technologies |
3rd Party Technologies |
Wizard Spider
|
Wizard Spider
|
Sandworm
|
Sandworm
|
What’s important to know:
- Day 1 and 2 of the MITRE Evaluation were for the Detection Test and Protection tests were conducted on Day 4.
- Of the 30 vendors that participated in the evaluation all but eight do not offer a comprehensive solution and did not have a Linux agent.
- Of the 30 vendors that participated eight of them did not participate in the protection test.
Protection Kill Chains Overlayed with Detections
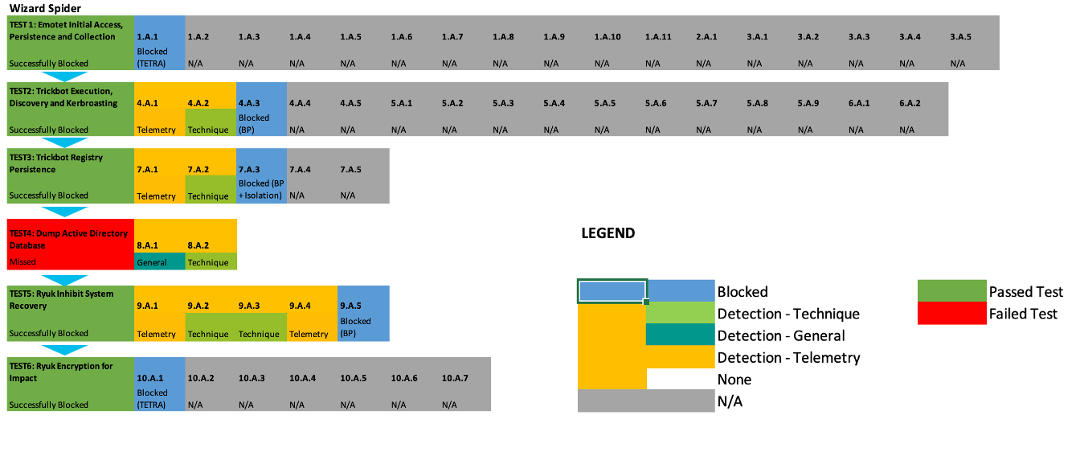

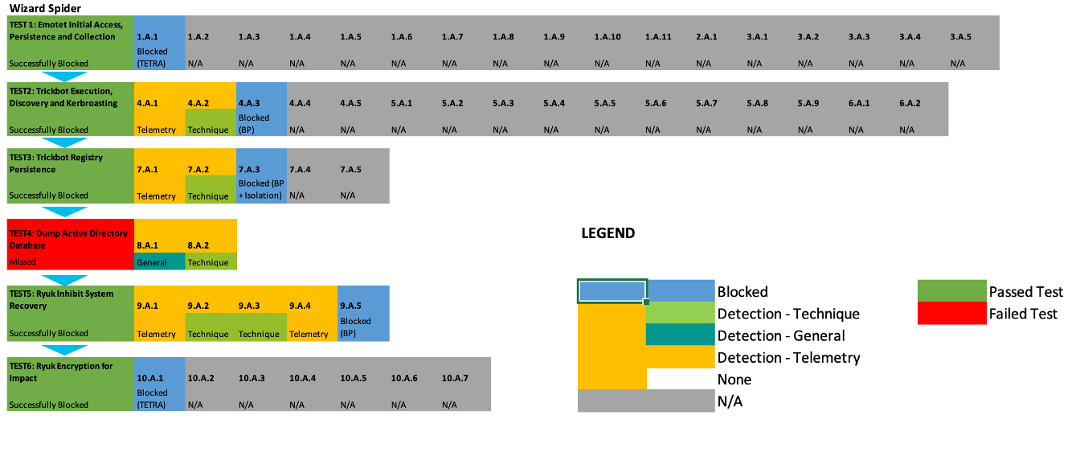
When it comes to protection, Cisco Secure Endpoint stopped both attack campaigns early in the kill chains and provided analytic detection at the MITRE ATT&CK level across each step of their respective kill chains. With real-time protection and analytics, a security analyst can remediate the threat with a reduced mean time to detection and response. Cisco Secure Endpoint blocked Wizard Spider at the start of the kill chain, however, an Active Directory database dump test was executed in Test 4. It’s important to remember that the protection tests are executed as independent unit tests; in this case it’s assumed the earlier tests were unsuccessfully blocked.
Cisco Secure Endpoint Analytic Coverage significantly improved in the 2022 Evaluation, allowing us to see the tactic or technique used at a more granular level. Cisco Secure Endpoint’s improved insights on the threat’s specific technique helped accelerate the mean time to detection and response.
Cisco Secure Endpoint had a significant number of detections at the first substeps of each phase in the Wizard Spider and Sandworm kill chain emulated in the MITRE Evaluation. Alert on potential threat actor activity was immediate quite early in the kill chain, which helped reduce attacker dwell time on the endpoint.
Cisco Secure Endpoint Behavioral Protection again played a critical role in identifying threats. We will continue to expand and develop Behavioral Protection for customers.
Links to Cisco’s MITRE Engenuity ATT&CK results:
- Scenario 1: Wizard Spider
- Scenario 2: Sandworm
- Protection Test
Cisco Secure Endpoint and MITRE ATT&CK: Why it matters to CISOs right now
Securing your endpoints has never been more critical, and you need endpoint security you can trust. Cisco Secure Endpoint is designed for those seeking endpoint resilience. Meeting security head-on requires adopting a comprehensive cloud-based endpoint protection solution for your secure remote worker, SASE, XDR, and Zero Trust architecture. We are the only endpoint security solution to deliver a cloud-native, built-in platform, Cisco SecureX, delivering XDR capabilities and more for better threat visibility, more intelligent investigations, and faster response.
Cisco has been recognized as a leader in endpoint security
- Strategic Leader in the 2nd annual AV-Comparatives EPR testing
- First Place in Radacti’s 2021 Endpoint Security Market Quadrant
- Approved Business Product Award by AV-Comparatives
See it for yourself
We know what you are facing, a world where malware is constantly evolving, and threats are becoming harder and harder to detect. The most advanced and riskiest threats that will eventually enter and wreak havoc in your network could potentially go undetected. Secure Endpoint provides comprehensive protection against any threat. This security software prevents breaches, blocks malware at the point of entry, and continuously monitors and analyzes file and process activity to rapidly detect, contain, and remediate threats that can evade front-line defenses.
To learn more about Cisco Secure Endpoint and see for yourself how it protects you against today’s threats, join our virtual threat hunting workshop or sign up for a free trial.
We’d love to hear what you think. Ask a Question, Comment Below, and Stay Connected with Cisco Secure on social!
Cisco Secure Social Channels
Instagram
Facebook
Twitter
LinkedIn

