
Diamond in the rough: Helping students discover their potential as jewelry designers
December 7, 2022
Explorations in the spam folder–Holiday Edition
December 8, 2022Cracking the Code to Security Resilience: Lessons from the Latest Cisco Security Outcomes Report

“There’s so much left to know, and I’m on the road to find out.” –Cat Stevens (Yusuf)
Two years ago, we asked the question: What actually works in cybersecurity?
Not what everyone’s doing—because there are plenty of cybersecurity reports out there that answer that question—but which data-backed practices lead to the outcomes we want to implement in cybersecurity strategies?
The result was the first Security Outcomes Report, in which we analyzed 25 cybersecurity practices against 11 desired outcomes. And thanks to a large international respondent group, together with the mighty data science powers of the Cyentia Institute, we got some good data that raised as many questions as it answered. Sure, we found some strong correlations between practices and outcomes, but why did they correlate?
Last year, our second report focused in on the top five most highly correlated practices and tried to reveal more detail that would give us some guidance on implementation. We found that certain types of technology infrastructure correlated more with those successful practices, and therefore with the outcomes we’re seeking. Is architecture really destiny when it comes to good security outcomes? It does appear to be the case, but we had more research ahead of us to be more confident in a statement that sweeping.
All the while, we’ve been listening to readers considering what they’d like to glean from this research. One big question was, “How do we turn these practices into management objectives?” In other words, now that we have some data on practices we should be implementing, how do we set measurable goals to do so? I’ve led workshops in the UK and in Colombia to help CISOs set their own objectives based on their risk management priorities, and we’ve worked to identify longer-term targets that require close alignment with business leaders.

Achieving security resilience
Another question that took a front-row seat in our presentations and just wouldn’t leave: the topic of cyber resilience, or security resilience. It’s almost reached the status of a buzzword in the security industry, but you can understand why it’s ubiquitous.
“Among the upheaval of the pandemic, political unrest, economic and climate turbulence, and war, everyone is struggling to find a new ‘business as usual’ state that includes being able to adapt better to the shaky ground beneath them.”
But what exactly is security resilience, anyway? What does it mean to security practitioners and executives around the world? And what are the associated cybersecurity outcomes that we can identify and correlate? We know it doesn’t simply mean preventing bad things from happening; that ship has sailed (and sunk). We also know that security resilience doesn’t always mean full recovery from an event or condition that has knocked you down. Rather, it means continuing to operate during an adverse situation, either at full or partial capacity, and mitigating the effects on stakeholders. Ideally speaking, security resilience also means learning from the experience and emerging stronger.
What’s new in Volume 3
Security resilience is the focus of the third volume of our Security Outcomes Report: Achieving Security Resilience. It tells us how 4,700 practitioners across 26 countries are prioritizing security resilience: what it means to them, what they’re doing successfully to achieve it, and what they’re struggling with. Once again, the data gives us interesting ideas to ponder.
A stronger security culture boosts resilience by as much as 46%. By “culture,” we don’t mean annual compliance-driven awareness training. Cybersecurity awareness is what you know; security culture is what you do. When organizations score better at being able to explain just what it is that they need to do in security and why, they make better decisions in line with their security values, and that leads to better overall security resilience.
It doesn’t matter how many people you have; it matters whether you have any of them available in reserve to respond to events. Organizations with a flexible pool of talent internally (or on standby externally) show anywhere from 11% to 15% improvement in resilience. Which makes sense, as a fully leveraged team will be strained if they have to work even harder to take on an incident.
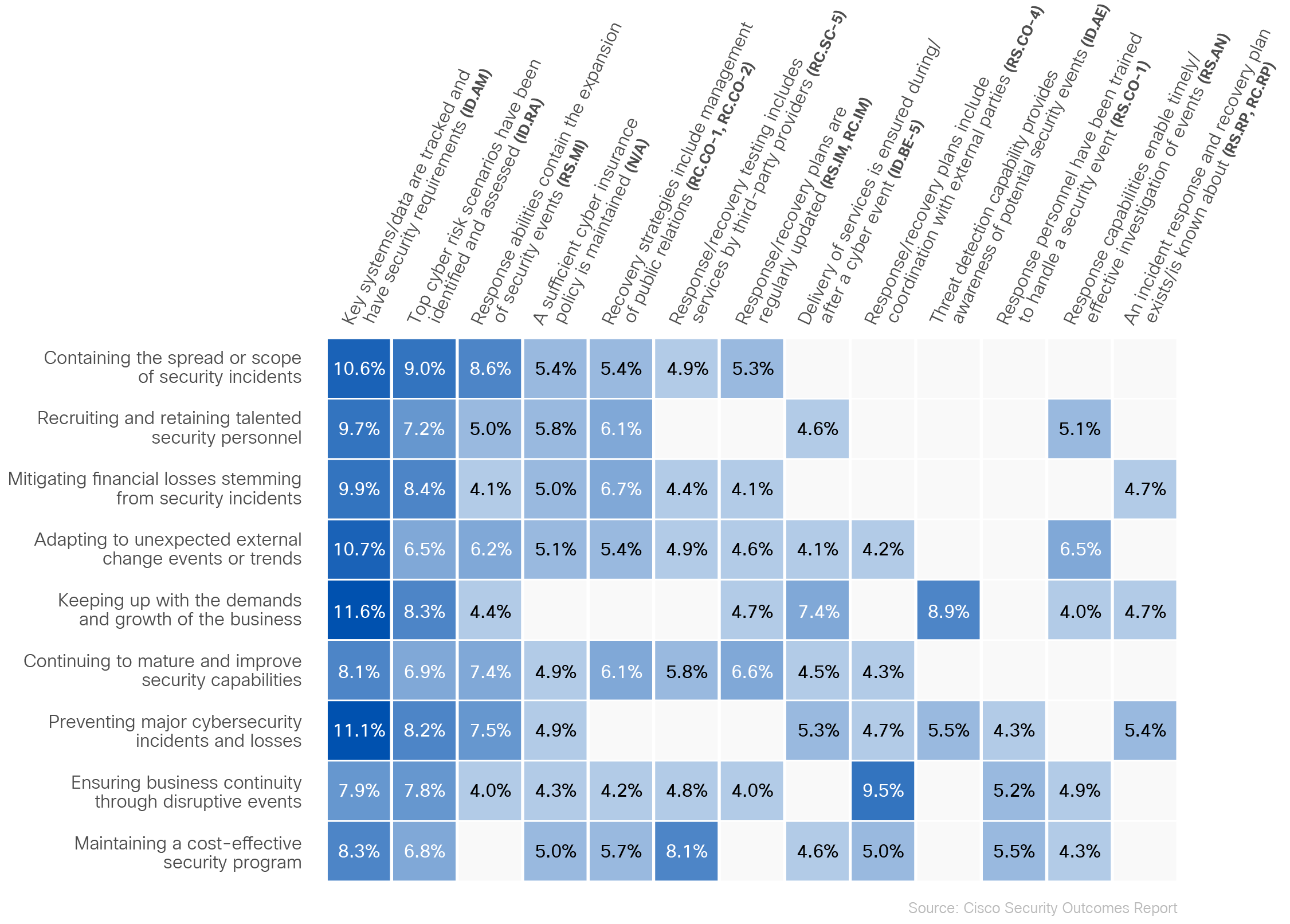
Because so many organizations around the world are looking to the NIST Cybersecurity Framework as a guidepost for cybersecurity practices, we also analyzed which NIST CSF capabilities correlated most strongly with our list of resilience outcomes. For example, our survey respondents that do a great job tracking key systems and data are almost 11% more likely to excel at containing the spread and scope of security incidents. From one angle, this seems like an obvious result, hardly worth mentioning. On the other hand, it’s worth presenting to your management some data that shows that investing in asset inventory solutions really does have long-range effects on your ability to stop an intrusion.
And there’s much more. The report identifies—and then explores—seven success factors that, if achieved, boost our measure of overall security resilience from the bottom 10th percentile to the top 10th percentile. These include establishing a security culture and properly resourcing response teams, among others.
I hope this introductory blog—the first in a series exploring this latest report—whets your appetite to read the report itself. And remember, we are always aiming to reveal the next undiscovered insight that leads to better security outcomes. Please share your feedback and research requests with us in the comments below, or talk to us at the next security conference.
For more insights like what you’ve seen in today’s blog take a look at the Security Outcomes Report, Volume 3: Achieving Security Resilience.
Explore more data-backed cybersecurity research and other blogs on security resilience:
We’d love to hear what you think. Ask a Question, Comment Below, and Stay Connected with Cisco Secure on social!
Cisco Secure Social Channels

