
Artificial Intelligence Improvement to Home Security
November 25, 2019
A New Day for Critical Infrastructure Security & Resilience
November 27, 2019Malvertising
Online advertising is an integral part of today’s internet experience. In many ways, ads are the lifeblood behind many websites, providing the necessary funding to keep sites running, as well as supporting the creation of new content.
While it may appear as though the ads that are displayed are just a component of the site you’re visiting, this isn’t often the case. Behind the scenes there is a complex network of advertisers, affiliates, and ad exchanges that bring the ads to you. A whole industry has built up around the process of serving up ads, by some estimates exceeding $100 billion in revenue per year. Tracking the sites a user visits and the ads they click on, alongside other metrics, has led to the tailored advertising experience we often see today.
These ads can run the gamut from amusing to annoying. The latter can be a source of frustration for users, with ads popping up while viewing a page, appearing in the middle of an article, or being masked as “sponsored content” that can sometimes be difficult to distinguish from the core content on a page.
In addition, many legitimate websites and content creators heavily rely on ad revenue as an income stream. This can cause even greater confusion for users trying to stay safe online, as legitimate sites may urge users to turn off any ad-blocking software they may have installed. Likewise, content creators and influencers are known to ask users to engage with their ads in order to support their work. Simply put, ad culture is everywhere online.
And those ads can be dangerous. Malicious advertising, or “malvertising” for short, has become a more common occurrence as bad actors have figured out how to infiltrate ad networks in order to serve up malicious content. And while there are steps that you can take, there is no simple, silver bullet to fully protect yourself and your organization from malvertising.
Today’s ad networks
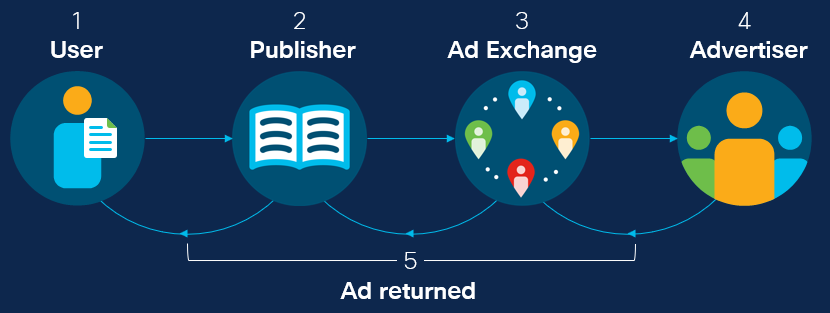
There are a variety of delivery methods for online advertising, though ad exchanges are one of the most common today. This process includes publishers who post the ads to the site, exchanges that facilitate bidding for ad placement, and advertisers who bid to win placement on the site.
At a basic level, you can look at this process as being similar to a car auction. The seller (web user) puts their car (ad space) up at an auction house (publisher). The auctioneer (ad exchange) opens bidding up to the potential buyers (advertisers). The highest bid ultimately wins the car, and the buyer pays the user with money (ad).
To be more specific, this process for serving ads works like this:
- A user requests a particular page that includes an ad space.
- A publisher collects information about the user and passes it to an ad exchange.
- The ad exchange passes the information available to advertisers and creates an auction placing an ad on the page.
- The advertisers determine if they have suitable ads and make bids for the ad space accordingly.
- The winning bid is passed back to the publisher, who displays the ad to the user.

The entire bidding process takes place in a fraction of a second. It’s so quick that multiple bids can be completed between the time a link is clicked and the page loads.
The data that drives the process—determining which ads advertisers bid for and how much they bid—is often the information gathered about the user. Geographic location, language, browser type and version, and operating system can commonly be determined when a page loads. If you add information gathered from third-party cookies, such as age and other demographics, far more information can be gathered as well.
Where things go wrong
From an advertiser’s perspective, ad exchanges can help facilitate cheaper ads that reach the customers that they want to reach. However, the bar is quite low in terms of who qualifies as an “advertiser.” In many ways this is necessary for smaller businesses and sellers to be able to get their ads easily distributed online. However, it also leaves the door open for bad actors.
Without significant vetting taking place on many advertising networks, it’s fairly straightforward for cyber criminals to enter these networks and bid for ad placement alongside legitimate advertisers. By doing so, these bad actors have the opportunity to place malicious ads in front of users.
Not only that, but a malicious advertiser can leverage the advantages gained by the information gathered about the user. For instance, if the malicious actor learns that the user is running an out-of-date version of the Google Chrome web browser they can place a bid and, if they win the auction, serve up a malicious ad that could exploit the vulnerable browser.
It’s also important to note that websites rely on the legitimacy and security of ad networks when utilizing them to display ads on their sites. There is very little that they can do to screen for malvertising. If a malicious ad is identified, website owners can technically request that it be removed, but that does little to protect already affected users. Because of this, it’s important that users not conflate the trust instilled in a particular website with the ads displayed in the site.
Redirection in malvertising
While more could be done, online advertising isn’t entirely a free-for-all, and some vetting does occur. That means a bad actor can’t necessarily send a user directly to a page with an exploit or a malicious payload without being found out.
As a result, attackers leverage redirection. In a nutshell, when a redirection is included in a URL or on a web page, the browser is told to go to another site to retrieve the content it is looking for. Frequently, malicious actors will redirect a user through a series of URLs before landing on the malicious page.
There are a variety of ways attackers can do this. One of the most common methods today is by using what are called 302 requests in HTTP. In these cases, the browser is told that the page they are looking for has temporarily been moved to another location and a new URL is provided.
In other cases, a redirection can be performed using HTML or JavaScript. There are even techniques, such as the JavaScript location.replace method, that don’t even leave a record in the browser’s history, masking the redirect from the user.
Payload delivery
Using this method, an attacker can attempt to distribute any sort of payload they wish. In many cases, the final content displaying on the user’s page is an ad that entices them to download adware or potentially unwanted applications (PUAs) that offer a service, but does so by displaying further ads.
In other cases, the malicious ad opens a window or alert that attempts to trick the user into thinking their software is out-of-date. However, if they attempt to install the fake update, they find themselves infected with malware.

However, what’s most concerning is the information that an attacker can glean from a user, through the ad exchange, can be used for active exploitation. For instance, an attacker can choose to only bid on ads that come from users running Internet Explorer. Obtaining the winning bid, the attacker can send an Adobe Flash Player exploit in their “ad.” If the version of Flash installed is out-of-date, the machine can be compromised without the user even clicking the ad. The attacker has exploited the browser right out of the gate, requiring zero interaction from the user apart from loading the page that contains the ad.

Protecting against malvertising
The simplest way to shield yourself from malvertising is to block ads and connections to third-party sites (sites beyond the specific domain in the URL). Ad blocking add-ons are available for most major browsers, and sometimes protections come baked in to modern browsers.
However, taking too aggressive a stance against ads can impact the performance of a web site. Sometimes it may break key features and components. Many sites now stop browsers with ad-blocking from viewing their site to begin with, requesting that the user disable it to view the site’s content. And in some cases, ad blocking software will allow certain ads through anyway, if the ad provider has paid the blocker to avoid them.
Given the current advertising network climate, there really isn’t a simple solution to protect against all forms of attack. Ultimately, a layered approach is the best defense against malicious advertising.
- Domain-level protections, such as those offered by Cisco Umbrella, will help to block redirects to domains that are known to be malicious, often stopping a series of redirects halfway through the chain.
- An endpoint protection application, such as AMP for Endpoints, can prevent malicious payloads from being installed onto a computer that encounters a malicious advertisement.
- Network Security appliances that include IPS signatures, like Next-Generation Intrusion Prevention System, can detect malicious activity such as exploit attempts against vulnerable software.
- Cisco’s Secure Internet Gateway and Web Security Appliance contain web scanning features that can prevent access to malicious websites.
Finally, if you’re looking for a deep dive into malvertising, how it works, and more of the latest techniques used by cyber criminals, check out Cisco Talos’ blog post on the topic, Malvertising: Online advertising’s darker side.
Enjoyed reading this Threat of the Month? Subscribe to the Threat of the Month blog series and get alerted when new blogs are published.
The post Malvertising appeared first on Cisco Blogs.

