For IT professionals: Privacy and security in Microsoft Teams
April 10, 2020
Improve virtual meetings and bring consultations online—here’s what’s new to Microsoft 365 in March
April 10, 2020Zero Trust framework to enable remote work
Zero Trust Assessment tool now live!
With such a large influx of employees working remotely, many of the traditional network-based security controls are unable to protect the organization. For many organizations, there are two options: route all remote traffic through a strained legacy network architecture, resulting in poor performance and user productivity; or relax restrictions and risk losing protection, control, and visibility. Many organizations are turning to Zero Trust security framework to better support remote work and manage risk.
The Zero Trust security framework helps organizations effectively meet these challenges by gating access to resources individually using granular access policies that take advantage of dynamic user and device risk signals and other telemetry to make more adaptive access decisions.
Support for your Zero Trust journey
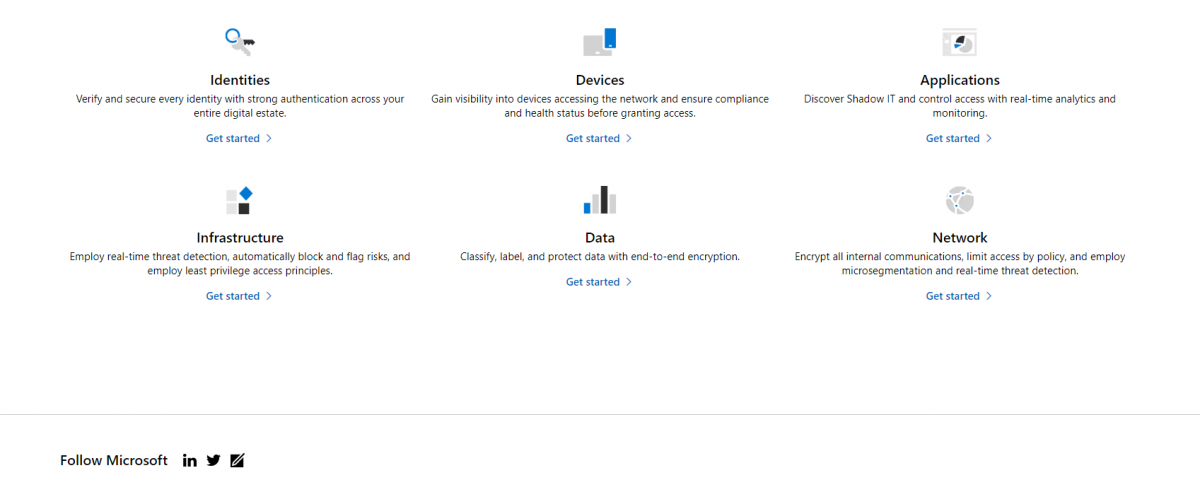
Getting started on your Zero Trust journey can be daunting, but we’re here to help. We’ve created the Microsoft Zero Trust Assessment tool to help you determine where you are in your Zero Trust journey. Our assessment tool will help you assess your readiness across identities, devices, apps, infrastructure, network and data, and then provide go-dos and deployment guidance to help you reach key milestones.
Every company is at a different stage of their Zero Trust journey. Given the current situation with remote work, maybe you are working to unify your identity management to enable single sign-on (SSO), or you are digging into projects like multi-factor authentication (MFA) or desktop virtualization. Maybe identity and device management are your top priorities right now. Every IT leader needs to define the priorities to enable productivity from anywhere across their organization’s workforce depending on the situation. We understand and we’re here to help.
We recently published Microsoft Zero Trust Maturity Model vision paper detailing the core principles of Zero Trust, along with our maturity model, which breaks down the top level requirements across each of the six foundational elements.
Upcoming, we’ll be publishing deployment guides for each of the foundational elements. Look out for additional guides in the Microsoft Security blog.
Learn more about Zero Trust and Microsoft Security.
Also, bookmark the Security blog to keep up with our expert coverage on security matters. And follow us at @MSFTSecurity for the latest news and updates on cybersecurity.
The post Zero Trust framework to enable remote work appeared first on Microsoft Malaysia News Center.