
Alludo’s subscription model equips businesses for success
October 12, 2022
Never negotiate your true self: Key lessons from the Autodesk Latinx Network lead
October 14, 2022COLLECTING OUR BREADCRUMBS (Pt. 2 of “Why Don’t You Go Dox Yourself?”)

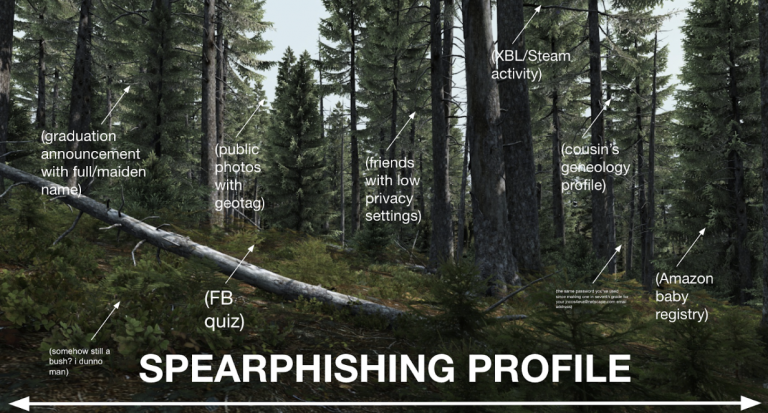
Sharing is caring… but on the internet, sharing can also be tricky! When we post something, we have to look at the forest and not just the trees. Doxxers usually start with one or two pieces of relatively innocent or public information, but by connecting the dots between those pieces they can build a frighteningly detailed picture of an individual.
Seemingly innocuous details can be pieced together into a much more personal profile when collected and leveraged to learn more. As one example, your wish list/wedding registry makes it easy for friends and family to get you gifts that you actually want, but could also be used to find out products/services you’re interested in as pretext (setting the scene) of a conversation or phishing email trying to gather more. You may have Google Alerts set up for your name (a great idea!), but this may not flag text in scanned documents such as school yearbooks, newspapers and other digitized paper records available online.

If the above sounds scary – don’t panic! Your first step in this auto-dox is going to be brainstorming as much personally identifying information (PII) shared online as possible. I suggest doing this either in a secure note or longhand. The goal is to write down all of the accounts/addresses/phone numbers that come to mind, as these are some of the top things that attackers will try to gather in their search. Start your list here:
- Your name: This can be your real name, as well as any other names you go by in public like a writing pseudonym, nickname, or stage name.
- Your phone number(s): Many social media networks let you look up friends through your contact book or by their phone number, and many other legitimate websites will use simple verification of your phone number as a way to prove your identity. An attacker can take advantage of both of these things. Don’t forget work numbers or old phone numbers!
- Your email address(es): This is the other main way to look up contacts on social media, and for most people it’s also the strongest common link between accounts. If you use a school or work email, there’s also a good chance it also contains part or all of your real name (like “first.lastname@school.edu”).
- Your social media: We share a ton on social media, and even if you’re careful about not sharing your real name or location, other information like where you go to school/work, what groups you’re a member of, who your friends are, and what you’re interested in can all help paint a picture of who you are.
- Your location: Previous and current home addresses are often used to verify identity even though many can be found online, so we’re going to use some free “data scraping” tools in our research to see what information is accessible. These sites collect public information like birth, death, and marriage records and make them searchable. There’s a good chance that there’s more than one person with your name unless it’s very unique, so these sites will usually let you add more information like a city, state or ZIP code to narrow down results.
- Your selfies and avatars: Sometimes getting access to private photos (especially sexytime pics) is the end goal of doxxing, but it can also be one of the ways to link different accounts. For example: Do you have your Facebook photos linked to your Tinder profile? Someone could use a reverse image search or site like TinEye.com to see where else you’ve shared the same pic. Newer sites like pimeyes.com even provide “fuzzy” search tools, where one photo of a person’s face can be used as a search for other, DIFFERENT photos of that person.
DEEPER DIVE: EMAIL ADDRESSES AND USER ACCOUNTS
Email addresses are an especially juicy target for someone trying to locate you, because most people only use one personal and maaaybe a second school or work email account. Those accounts are tied to all our other online identities and often double as our username for logging in.
- If you already use a password manager, you’re ahead of the game! Review the current accounts and credentials that you’ve already added. Depending on the tool you use, this may also notify you of reused or breached passwords that have appeared in previous hacks. And, if you’re not using a password manager, now would be an excellent time to check some of the available options and set one up! This way you can add your collected credentials and update weak or reused passwords as you go.
- Speaking of breached passwords, HaveIBeenPwned lets you search an email or phone number to see if it appears in their breached data database. And don’t be surprised if one (or several) of your accounts show up here – with more than 11 BILLION accounts currently collected, the odds are likely you’ll find something. Note it for now and update the password and enable strong authentication (more on this later).
- You can enter a username or email address on NameChk.com, and it will quickly search a bunch of different services and show you where that username has been registered.
- You can search your email inbox for common new account subject lines to find them manually. Try searching combinations of keywords: “confirm”, “activate”, “verify”, “subscription”, “account”, etc. (And if you’ve never checked out Google’s search operators, you can get even more specific about what to include or exclude.
- Check what information is publicly visible on these collected sites. Do you have a wishlist on Amazon? An “anonymous” Reddit account with the same username as your Pinterest? An abandoned MySpace or Tumblr with outdated privacy settings? See if you can disable or restrict public viewing — some sites like Facebook make it easy to change privacy on old posts.
- Facebook, LinkedIn and other social networks often have a “View As” option that lets you see your profile as a stranger, a friend of a friend, or a direct friend. Look at each of these views and consider if you want that information public and searchable. Sometimes these settings can be sneaky! On one review after I set all my pictures on Facebook to private, I tested visiting my page as a stranger and realized that my “featured” pics had been set to public without my noticing.
When you finish this process, you will likely have dozens or even hundreds of “breadcrumbs” between your account list and search results. Read through your list again, and we’re going to sort it into three categories:
- Critical: This is for accounts with the most private or potentially damaging information in them – services like your online patient portal for the doctor with your medical information, or financial accounts that may include your banking information or social security number. As these represent the greatest risk if compromised, they’re at the top of the list to fix.
- Wanted: This is for everything else that you want to keep but isn’t nearly as sensitive as the first category. News site logins, loyalty club websites and special interest forums may all be accounts you want to maintain, so they’ll also be in the queue behind our top priorities.
- Unwanted: As mentioned previously, you’ll likely unearth some forgotten or abandoned accounts that you no longer need. If you never need to log into that account again, take the time to cancel or delete it. If your data is no longer stored by a service it becomes much more difficult for an attacker to find it! You may also discover a surprising amount of your information is available through people search services and data brokers that you don’t want shared, and we’ll start working on next.
Great job! You’ve already got a much better idea of what people can learn about you than most folks ever do, and are well on your way to cleaning up your online footprint. In our next step, we’ll start locking down everything that you want to keep!
P.S. If you’re enjoying this process and value keeping people safe online, please check out our open roles at Cisco Secure.
We’d love to hear what you think. Ask a Question, Comment Below, and Stay Connected with Cisco Secure on social!
Cisco Secure Social Channels

